How the Sony hacks made the US go into a cyber war frenzy
Is this really how we’ll deal with cyberattacks in the future?
(this article was previously published in Dutch on Datanews)
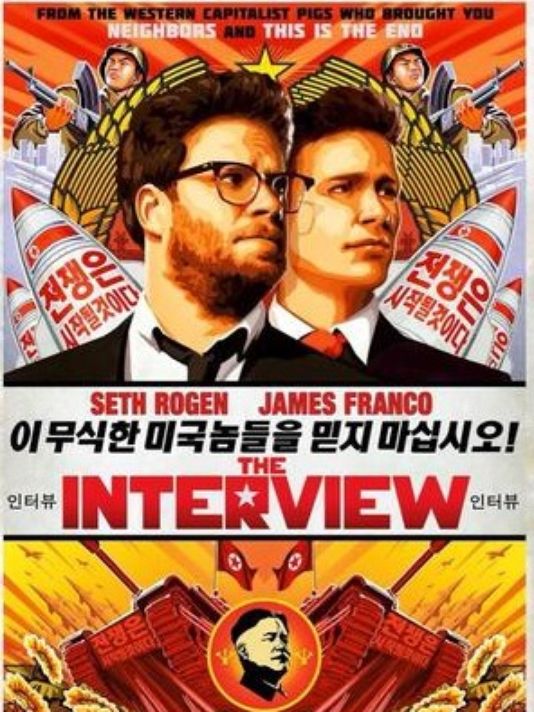
Whether the Interview is a good movie or not is debatable, but we can all agree that it has caused a lot of commotion. Not only did it enjoy the weirdest marketing campaign in movie history and caused a diplomatic riot, it also set some special precedents, making many think the Cyberwar has commenced.
The events unfolding in the past few months could have been a movie on its own. Two comics make a silly movie about assassinating the current North-Korean dictator. The actual North-Korean leader is offended. Coincidentally the film production house is met with a heavy cyber attack destroying their entire systems. Theatres are threatened to “not forget” 9/11 in case they would play the movie. The theatres and production companies cowardly withdraw, which is met with a public outcry, and the film is released anyway with alternative means. The FBI is quick to point the finger to North-Korea, sanctions the country, while the North-Korean internet ‘coincidentally’ also goes offline. Obama is called a monkey, and in between people start remembering both country also have nuclear weapons.
We’ll have to wait for the DVD-release and the next Wikileaks to see the behind-the-scenes footage, but for now it has all been very amusing.
While the dust is settling, it’s interesting to have a closer look at what the Interview and the ‘Sony Hack’ has set in motion.
Playing the blame game with North-Korea
In the entire analysis of the Sony Hack, the diplomatic aspect is the most striking.
Already after a few days the FBI concluded the cyberattack and the threats made could be attributed to North-Korea, based on flimsy evidence.
A lot of doubt has been cast on this attribution by several experts.
While the FBI refuses to admit how exactly the trail of its investigation leads to North-Korea, most of the evidence it gives or would credibly be able to give, is indirect circumstantial evidence according to experts.
While one would hope the US wouldn’t make such harsh accusations without a solid backing, we mustn’t forget the assumed Weapons of Mass Destruction in Iraq. Back then the US was also very sure of what later proved to be false accusations.
North-Korea denied the responsibility for the attack, but the New York Times saw a half confession in North-Korea’s statement that the attacks were ‘righteous deed of supporters and sympathizers’.
Was North-Korea aware these attacks were being launched? And is a country also responsible when it sees evil being done and doesn’t try to stop it?
The US turned down North-Korea’s offer to launch a joint investigation, and went in the offence. The 2nd of January it raised sanctions on the most heavily sanctioned country in the world. This was a world first, effectively being the first time the US punished a country for a cyber attack on an American company.
Very ‘coincidentally’ the North-Korean internet also went offline.
The US denied any role, although fingers can also be pointed to a country with suspicious motives. Such actions would be giving North-Korea just as much right to strike back covertly.
North-Korea currently only responded furiously, with press releases like “U.S. Urged to Honestly Apologize to Mankind for Its Evil Doing before Groundlessly Pulling up Others”.
Whether the US has proof or not, according to Allan Friedman, researcher at the George Washington University’s Cyber Security Policy Research Institute, it is a smart diplomatic strategy to be overconfident in assigning blame for the cyber attacks. To prevent precedents from being made, it’s best to discourage other states from engaging in similar behaviour by punishing North-Korea, even when lacking concrete proof.
Is this the beginning of a Cyber War?
A lot of talk in popular media mentions cyberwar when referring to the Sony hacks, but was the crippling of a company really an act of war?
This lack of certainty on attribution is already vital to define this attack as an act of war. It is almost impossible to speak of a cyberwar in such a covert domain since wars are traditionally only fought between nations.
But let’s assume for the sake of the argument the FBI is right and North-Korea was behind the hacks.
When treating the term ‘war’ literally, we have to look at whether this was a use of force, as described in the United Nations Charter. It’s forbidden to use force, unless when used in self-defense, or when permitted through a UN Security Council resolution. If you don’t have that justification, you might have started a war.
Based on a lot of discussions and precedents, it has sort or less been agreed what such a forbidden use of force can be; inflicting harm with such a scope, duration and intensity that it threatens the territorial integrity or political independence of a state.
So when a lot of people die, and the national security is threatened, it’s a use of force. Makes you think twice about the impact of crippling a company that, according to Dr. Evil in Saturday Night Live ‘hasn’t been relevant since the Walkman’.
But even here, when it comes to war, the cyber domain is a grey zone. A difficult domain where no clear lines can be drawn about what is enough ‘damage’ to regard something an act of war. There’s no international legislation, there are no precedents and thus there are no norms telling us when we feel enough damage is done for something to be classified a use of force.
Something Pentagon Press Secretary Rear Adm. John Kirby also repeated, with the plea to urgently set up international rules.
A lack of such international legislation and precedents also means a country can attack another, and a country like the US can reply at will. Its permissibility depends on whether the international community condemns such actions or not, shaping the norms as a consequence.
But it would also mean this would be where the line is drawn for future reference. The US knows better not to turn these hacks into the great ‘cyber Pearl Harbour’. As cyberwar expert Peter Singer said on the Motherboard, ‘we’re not going to war with North-Korea because Angelina Jolie is angry at some Sony Executive’.
At the same time the US is taking the matter very seriously, treating the hack on American soil as a matter of national interest.
Especially after threats were also made.
Cyberterrorisme?
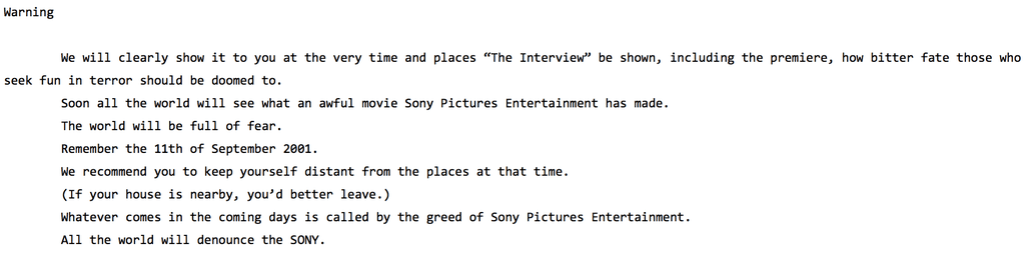
“The World will be full of fear. Remember the 11th of September 2001. We recommend you to keep yourself distant from the places [where the movie is shown] at that time.”
The threats made by the hackerscollective responsible for the Sony Hacks apparently left a great impression that made many speak of ‘Cyberterrorism’.
The term terrorism is used frequent to describe any threat without a clear state actor, solving the attribution conundrum. The concept of the ‘war on terror’ is still a controversial way to circumvent the traditional paradigm of “wars are only fought between nations”. The reminder of the US’ collective trauma made the nation immediately up in arms.
Sony added fuel to the fire by caving, and allowing the film to be withdrawn from 180.000 theatres. Allowing fear to rule and complying with threats is how to ‘let the terrorists win’. As Peter Singer also said, the way Sony handled the entire ordeal has turned into a case study on how NOT to respond to terrorist threats. Especially when these hackers have not shown any capability to carry out anything remotely physically damaging.
Such scaremongering comes with ignorance on what damage cyber attacks can actually cause.
Did Sony have the right to panic?
Coming back to the use of force, there has thus far not been an overt cyber attack that could be classified as an act of war, even though the possibility exists. With the Aurora Project the US even proved how much physical damage a cyber attack can cause.
The damage done to Sony was nowhere near comparable to such physical damage.
100 Terabyte worth of data was stolen, as well as ‘wiper malware’ was used. This type of malware destroyed Sony’s internal systems (from production planning to human resources). This meant the company has to replace all their systems, paralyzing it for a while.
But this type of malware was also used in the South-Korean DarkSeoul case attacking banks, and the Saoudi Aramco case attacking the oil company. Lack of international regulations made these cases also hard to classify and respond to. But while they also caused a lot of commotion, they were not considered an act of war or terrorism, nor did it result in a witch hunt.
Important to remember is Sony also has a history of leaks and security breaches. The Playstation hack of 2011 is still fresh, where 2,2 million credit card details were stolen through the Playstation network.
Yet Sony hit the panic button this time, when critical company details were compromised. The perceived gravitas was beneficial for Sony, where the attack seemed so sophisticated they would not have been able to prevent it. The idea of being ‘hacked by a dictator’ added to their benefit, where they could claim ‘circumstances beyond their control’ when they would be put on trial.
It is no secret though that Sony’s security prescriptions were flawed, with the leaks even showing one of the CEO’s having an embarrassingly simple password. The panic ruled in their favour.
Bruce Schneier concludes that Sony wasn’t afraid of the damage the hackers would do in a terrorist attack, but feared for the commercial damage to the company.
The leaked information is probably being sold to the highest bidder by now.
Such a perspective makes one think about the role North-Korea played in all of this. Did they really cripple a multibillion dollar company as a sadistic move because their Supreme Leader was insulted by a movie?
It is scary not to be able to tell whether an attack came from a small group of criminals playing a mean prank by releasing a threat, or an entire country. It’s causing big countries like the US to lose their cool.
Not only was the damage not that significant, was the target no matter of national security, but harsh accusations were made and sanctions were lifted against a country based on very flimsy evidence.
A long term vision is necessary to protect against cyber attacks towards the future. Especially now that the Aurora target list of American critical infrastructure was leaked.
It is highly doubtful though whether flexing some muscles and scaremongering will help to win a ‘war’ against anonymous hackers.
Biggest digital release ever
The conspiracy theorist would expose this entire debacle as an amazing marketing campaign for a movie.
Sow fear, boost patriotism, create a Barbara Streisand effect where people want to see this hyped movie. Release the movie and have everyone watch it as their personal act of rebellion. ‘That’s my kind of war on terror’ was tweeted by those proudly watching the movie.
Causing a diplomatic riot to promote a film, nothing is surprising anymore in this day and age. And whether it was deliberate or not, the film can also claim the record of the biggest digital release ever. With 15 million dollars income in the first 4 days, the movie finally catapulted the movie industry in the digital age.
The transition from 2014 to 2015 was one of many interesting phenomena. The biggest hack on American soil, fear of cyberwar and cyberterrorism, a diplomatic riot between two nuclear countries, the biggest online movie release,… All centred around one movie: The Interview. The film is definitely one for the history books, although probably not for its content.





Leave a comment