cyberwar digital society disinformation Israel-Palestine platform governance protests social media
-
Factchecking the online ‘rape academy’ discourse; on the tension between accuracy and activism
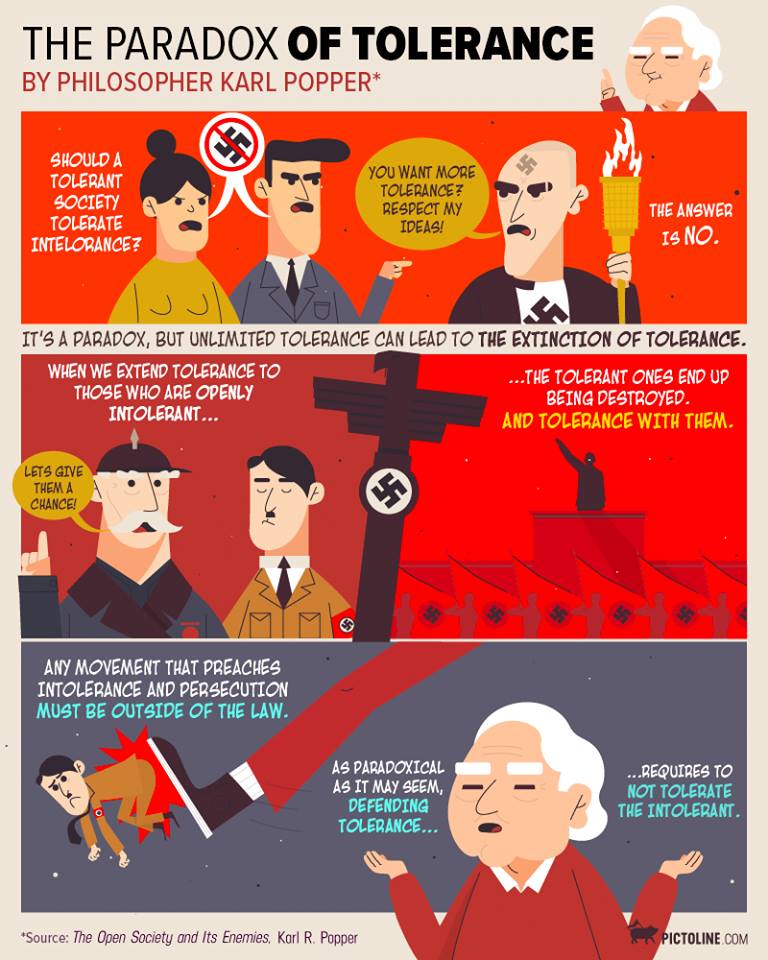
Over the weekend the story of an “online rape academy” went viral on social media, following an investigative reporting by CNN about an online network of men that exchanges tips to drug and rape their partners. The article was lengthy and detailed, and somewhere in the copy, remix and transform process of the online news cycle, details of the story got distorted and mischaracterized. A networked discussion ensued on the importance of accuracy in sharing such stories and led to outrage by some who experienced this as a call for purity. This discourse surfaces a common tension on social media between accuracy and activist intentions. In this piece I reflect on this tension, and provide insights on how those accuracy conflicts are shaped by platform mediated in-group out-group dynamics.
First the facts: on 26th March 2026 CNN reporters published a reporting titled ‘Exposing a global ‘rape academy’’ as part of its ‘As Equals’ investigation on gender inequality. Mid April, many social media content creators started sharing the report, of which many started claiming 62 million men were participating in an ‘online rape academy’.

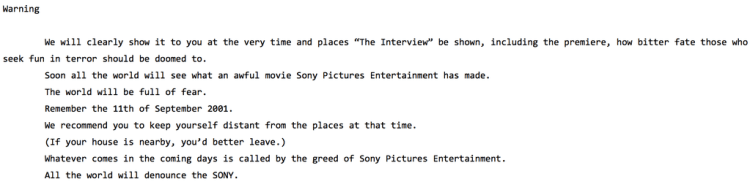
(this image was circulated widely on Twitter and Instagram)
Some corrections ensued, saying there were “only” 62 million visits to the rape academy, not 62 million men, which led to outrage with other netizens.

(comic by @mrJesseDuquette)
But this still did not accurate reflect the report, as there were no 62 million visitors to some “online rape academy”. In the CNN article, the “academy” term is used to describe a Telegram chatgroup with a few thousand members where users exchange tips to drug and rape their partner. The 62 million number refers to the amount of visits to the Motherless website, a porn site that hosts some of the #sleep and #eyecheck content that this online network posted on, but the website has a lot of other pornography categories that can be found on regular porn websites.
Righteous outrage
It is possible that the secondary sources skewing the number in the reporting didn’t properly read the article, or that they willfully inflated it to generate more clicks. It is also possible they didn’t think the number was important to factcheck before spreading it or be nuanced about. The Telegram group CNN found is just one of many that keep being discovered, where men exchange advice to rape women or share non-consensual sexual images. Dominique Pelicot’s group, the man who let his wife Gisele Pelicot be raped by 70+ men, is one of the most notorious ones and sparked international interest in the existence of such networks.
Furthermore, the Motherless website is not an innocent porn platform. It claims to be a ‘moral free file host where anything legal is hosted forever’, and many victims of revenge porn have found it near impossible to get content removed on the platform. As the New Feminist reports, the site also has a ton of women-degrading content and thousands of videos living under tags that show the sexual acts were likely non-consensual. Furthermore, the New Feminist shows that its architectures allow men who share similar (disturbing) preferences to find each other and move to encrypted channels like Telegram, making the porn site more of a ‘shop window’ leading people into darker backrooms.
The pushback against internet users correcting this 62million men number is therefore not difficult to comprehend. Discourse that pivots from sexual violence against women to accuracy of numbers can take attention away from the very real issues at hand. The way our algorithmized online ecosystems functions is that conflict breeds virality, which means a correction can become more visible than the actual content that is being corrected. This indignation over inaccuracy can inadvertently overshadow the indignation over the fact that there are many men worldwide exchanging tips on raping women and getting away with it.
The accuracy-activism tension
I learned the importance of not disrupting activist efforts with a factcheck for the first time when I used my Instagram account to factcheck a rumor in 2022 that 15.000 protesters in Iran were getting sentenced to death because of the Women, Life, Freedom protests. In reality ‘only’ 5 protesters had been sentenced to death and 15.000 protesters had been arrested, and called upon by some members of the Iranian parliament to be executed. I thought it was important to help factcheck this rumor, but Iranian activists made me aware that this factcheck is not at all helping the movement, as it is seeding doubts over the atrocities the regime is committing (which only escalated further, as in January 2026 estimations speculate up to 20.000 Iranian protesters were murdered by the regime in the span of a few days). What good does it do to demand factual purity from protester who are faced with a violent regime?
It made me reflect on what I was actually contributing to these activist movements by wagging the finger to keep things as factual as possible.
Despite these experiences, I still believe accuracy and factuality remain very important. Letting the importance of truthfulness fade is a slippery slope. This in turn can be weaponized by actors whose best interest is to not need to provide evidence for their claims. This happens often with far-right actors who inflate statistics on for example immigrant crime.
Even the skewed numbers of the ‘rape academy’ can be wielded by actors to seed moral panic over the dangers of the internet in their efforts to limit and control access to the internet. Efforts that disproportionately affect Sex Workers who are the first to get censored. There is of course a wider conversation to be had about the responsibilities of such porn platforms and messaging apps like Telegram that I will not get into for this piece (I wrote about it here before ) but certain efforts to mitigate these threats are worrisome for the future existence of a free and open web, and I refer to the work of Taylor Lorenz and Mike Masnick to know more why legal proposals in (among others) the US are very problematic.
How correctors gets othered
There is still a huge need for actors in the ecosystem that can monitor and provide reliable facts. Factcheckers and media that holds itself to a journalistic standard fulfill such an important role. Corrections by “In-group” members also hold a very important function, as research shows that due to fact-value entanglements, people are more likely to trust peers who share their values. Left-wing activists such as Christian Divyne have tried very hard to stress the importance of accuracy while highlighting the pervasiveness of sexual violence, but they still got attacked by their peers for their correction.
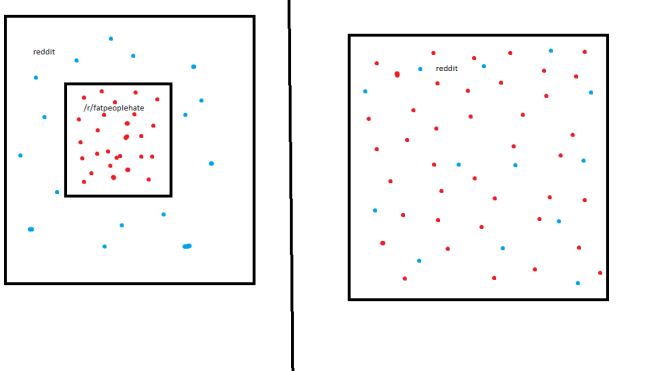
Apart from the indignation people feel about the broader issues at hand, it is not surprising that those correcting receive pushback in the existing information environment. I showed in one of my PhD papers how the threat that such in-group corrections get weaponized by an out-group (real or imagined) actively shapes users’ social norm practices on platforms like Twitter. I saw how participants in climate change discussions held back on publicly correcting in-group members or had been reprimanded for doing so, as they were aware that their conversations were being monitored by out-groups and instrumentalized to discredit the solutions to, or even the existence of anthropogenic climate change.
Users are not necessarily the only ones to blame for this dynamic where in-group members attempt to close the ranks, the openness of the online ecosystem plays a role in this. I theorized in my PhD thesis that the ‘external visibility’ on a platform, or the possibility that content is made visible outside of its own context, contributes to the formation of in-out groups. On platforms where potentially all eyes of every user observe such corrections, whatever users say can lead others to push them into a camp for or against their beliefs. It leads people to fortify positions; if I see that you disagree with people I consider my in-group, I may consider you part of an imagined out-group. Well-intended corrections can thus polarize groups.
Factlessness muddies the waters
Being afraid to dissent and correct peers is however problematic as it can lead to spirals of silence and groupthink. I have dedicated a few years between 2020 and 2023 to factchecking misinformation (see my older blogpost on this experience), and was always one to stress how “accuracy matters” in your activism.
This mostly came from a place to re-focus conspiracists who were mad about legitimate issues using bullshit arguments. Naomi Klein wrote a great piece about the protests against the World Economic Forum’s Great Reset plan, which was mostly designed to protect capitalist interests. Valid objections against the WEF got mixed up with conspiracies how this Great Reset had orchestrated the COVID-19 pandemic to take away everyone’s freedom. Klein called it the Great Reset conspiracy smoothie, warning us about the dangers of valid activism getting mixed in with baseless theories that muddies the waters of said activism.
I have since learned that calling for accuracy can also muddy the waters of legitimate activism. Demanding purity before anyone speaks out is part of a larger issue, especially in left-wing circles, that activists who don’t get every point 100% right, will be shunned and demanded to “do better” and potentially have their broader point invalidated.
Of course, if netizens had just used the right number in the first place, it wouldn’t need to be corrected. Such errors however happen as news trickle down, and while they still warrant correction, those corrections should always make sure the message does not get lost. This is not an easy feat in algorithmic platforms, as the correction can easily become the new story that pushes users to opposite sides of a discourse.
These dynamics won’t disappear as long as we’re left with platforms that reward conflict with visibility. The best we can do for now is try to navigate them gracefully with good faith towards each others’ intentions and refocus on the broader shared goals.
-
The Eurovision Song Contest as an information war battlefield

This article originally appeared in Dutch in SamPol.
The presence of Israel in the 2024 Eurovision song contest has generated a lot of protest, but Israel’s participation is an important part of its ‘Hasbara’ strategy to keep being seen as a rational democratic actor.
Military and political strategists have long known that a war is not just about tactical military victories. To ultimately emerge as the winner, it is also important to have international support for your struggle.
Israel is certainly well aware of that. Since the atrocities committed by Hamas on October 7, the country has continued to count on sympathy for its military actions in Gaza, which are considered by an increasing number of experts to be disproportionate and genocidal . Israel’s atrocities are meeting with widespread resistance worldwide, with students occupying university campuses in protest in the United States—and also in my own country Belgium. Yet military contributions continue to flow from countries like the United States, and the European Union remains painfully lenient toward Israel.
To generate international support, Israel possesses notorious and well- documented information warfare capabilities, sometimes referred to as ‘Hasbara’. Literally translated as ‘explaining’, Hasbara serves to influence international public opinion in Israel’s favor and maintain global support for its policies. In 2024, a Hasbara budget of approximately 17 million euros was allocated as part of its ‘public and cultural diplomacy’.
In this context, the Eurovision Song Contest comes into the picture. Although often regarded as a frivolous song contest, the Eurovision Song Contest has a significant cultural and political impact. Every year, some 160 million people worldwide watch the competition, which was launched in 1956 to unite the region following the trauma of World War II. Israel has long used the LGBTQI+-friendly contest to position itself as a Western democracy that embraces liberal values. Consider, for example, how the Israeli Dana International was the contest’s first transgender winner in 1998. Participation in the Eurovision Song Contest can therefore be seen as a Hasbara practice aimed at overshadowing Israel’s image as an occupier. This practice is also sometimes referred to as ‘ artwashing ‘ and ‘ pinkwashing ‘.
This year, protestors put immense pressure on the song contest to prevent the country from participating and thereby normalize itself, while they violate human rights in the Gaza Strip. The organizer refused an exclusion by clinging desperately to the ‘apolitical’ nature of the contest, even though this did not really align with the earlier decision to exclude Russia within a week of its invasion of Ukraine in 2022.
To further reinforce this normalization, Israel campaigned fervently this year for Eden Golan, the Israeli candidate in the competition. They relied on billboards, social media advertisements, messages via embassies , and pro-Israeli influencers. This was accompanied by thinly veiled messages that a vote for Eden is a vote against antisemitism. An article by the Israeli news site Y-net revealed that the Israeli government also engaged in targeted advertising to expose certain Israel-sympathizing countries and internet users, as well as journalists and opinion leaders, to videos in which Eden Golan addressed them in their own languages to vote for her. Unprecedented for the Eurovision Song Contest.
Israel ultimately finished second in the public vote with a total of around 323 televotes. It is difficult to predict to what extent those votes reflect genuine appreciation for the song or indicate sympathy for the country. We know from previous research into Eurovision voting behavior that about 36% of the average voter cites reasons for voting other than the quality of a song. That ‘political voting’ may also have led to the Ukrainian victory in 2022. However, the number of votes for Israel could also have been heavily inflated by votes deliberately attempting to make support for Israel appear larger than it is in real life. Far-right allies across Europe have already made it clear on X (formerly Twitter) that they normally never watch Eurovision, but voted for Israel at least 20 times this year (the maximum number of votes per bank card). Meanwhile, the Slovenian public broadcaster has also requested an investigation by the EBU, as there were reportedly a suspiciously high number of new online voters.
Despite the fact that Israel did not win, the high score was used by Israeli spokespersons as a misplaced ‘poll’ to demonstrate just how popular the country still is. In my native Belgium, too, politicians like Theo Francken used the vote as an example of how a ‘silent majority’ of Belgians still supports Israel. In this way, a song contest is instrumentalized into an information war to create the impression that a country accused of genocide does indeed enjoy popular support.
Of course, we do not know to what extent the Hasbara campaign contributed to the Eurovision victory, or whether it influences political opinion tout court. Opinions on the conflict within Europe remain deeply divided, with a silent majority appearing primarily to want to see an end to the suffering of people in the region. Research also shows that Israel’s information warfare tactics may even be counterproductive by polarizing societies into groups that are either *with* or *against* Israel. Paradoxically, this would have led to greater solidarity with the Palestinians in the past. Similarly, Israel’s stubborn participation in Eurovision made a large group of viewers more aware of the opposition to Israel, which they might otherwise have heard of only on the periphery.
Although the end to the atrocities in Gaza currently seems far off, Israel may currently be digging its own grave with aggressive Hasbara campaigns, forcing itself into a song competition that was supposed to be about peace and unity.
-
The threat of disinformation can be worse than disinformation itself

This article originally appeared in Dutch for SamPol Magazine.
As several countries have introduced new legislation to put a stop to disinformation, those laws can also be abused to silence the independent press.
According to the World Economic Forum, “AI-generated disinformation” will be the biggest threat for 2024. For its Global Risks report, experts and policymakers are annually asked to look into their crystal ball and predict the state of the world. In the 2023 report, disinformation was still nowhere to be seen in the top ten, but this year it even surpassed “extreme weather events,” which has dangled (appropriately) in the top three for a decade.
This incredible rise in the threat of disinformation is curious, yet not unexpected. Some 4 billion people will vote in democratic elections in 2024; citizens in the U.S., India, Indonesia, Mexico, all of Europe and, of course my country Belgium, among others, will be casting their vote. And this after a year of dizzying AI developments where ever more realistic images and texts are artificially generated, in an era where, according to the Digital News Report, there is a global record of news avoiders. It seems like a perfect storm.
The fear of disinformation focuses most on elections because it is a moment where an opinion gains real power in the form of a vote. Influencing that opinion with lies, rumors and half-truths could lead to drastic shifts in power. However, it is difficult to measure what impact disinformation effectively has on such an opinion shift; a political vote does not simply change quickly because of a lie. Time and again, researchers find few significant correlations between fake news and election results, only that the convinced become even more convinced.
So we should take this threat of disinformation for power shifts with a grain of salt, and certainly the AI factor. Some politicians keep sharing obvious satire or poorly photoshopped disinfo over and over again, which passes almost silently among their constituents. What does that say about where the problem really lies?
The threat of disinformation can also have unintended consequences. Indeed, several studies show that widespread fear of disinformation actually leads to increased distrust in established media and even a reduced ability to identify disinfo. A “backfire effect” that has long been warned about when media literacy is based solely on increasing skepticism, and not on regaining trust in journalism and science.
Moreover, the threat of disinformation can also lead to a reaction that becomes more dangerous than the actual effects of disinformation. There, too, scholars found that greater fear of disinformation leads to greater support for undemocratic interventions. Several countries have created new legislation in recent years to call a halt to disinformation. But “fake news” is often not clearly defined. As a result, these laws can also be abused to silence independent press. According to the Committee to Protect Journalists, some 39 reporters worldwide have even been imprisoned by this type of legislation.
In Europe the Digital Services Act (DSA) entered into force on Feb. 17. This vital legislation imposes certain much-needed transparency obligations on VLOPS (euro-lingo for Very Large Online Platforms) and gives users more opportunities to appeal moderation decisions made by the platforms. However, the legislation can also be used as a blunt instrument by platforms when they are required to engage in “risk mediation”.
This was made clear recently when Thierry Breton invoked DSA obligations around harmful content when hate speech and disinformation spread on various social media platforms following Hamas’ Oct. 7 attacks on Israel. Research by NGOs such as Human Rights Watch and the Arab Center for the Advancement of Social Media found that platforms like Meta systematically silenced voices advocating for human rights in Gaza during that period. They were lumped into the same category of “Hamas glorification”. Although the DSA has various provisions and safeguards against unilateral and political interventions, a threat of legal obligations by zealous bureaucrats can lead to the hasty removal of content by the platforms.
Disinformation can certainly pollute debates, protests and legit criticism; it is the Achilles heel of liberal democracies that value free speech. That openness is also eagerly exploited by those who do not care about the importance of keeping the public space open. But with too narrow a restriction on freedom of speech, one can also stifle those who raise social injustice. The biggest mistake that can be made is to suppress legitimate criticism as a ‘precaution’.
There are unpleasant conclusions to be drawn from the WEF forecast, where legitimate concerns such as the “cost of living” and the “housing crisis” drop in the rankings and are replaced by the threat of disinformation. If we really want to protect elections against undemocratic actors, it doesn’t help to attribute social unrest to an allegedly deceived public. That kind of thinking leads to simple solutions that can make complex problems worse.
-
“Play my damn song!” Social norm conflict over Spotify’s Jam feature
It had been a while since i’d been to a house party where we played music and danced. Back in the days (mostly pre-pandemic), houseparties with my predominantly Belgian friends would revolve around one laptop where people would add songs, or one phone that would get passed around. When folks would start dancing and hyperfocussing on the music, there would be several contenders for what we dubbed “DJ internet”, adding songs to the queue on Youtube and later Spotify. Certain norms started forming at our parties that only became fully clear to me last night at a new year’s eve party, as those hidden rules underlying ‘our’ party clashed with other norms. The affordances of Spotify’s new Jam function played an important shaping role.
To set the scene: I went to a New Year’s eve party in Brussels hosted by one of my best Belgian friends and her Mexican partner with whom she was about to move in. The mix of guests was thus Belgian and Mexican, with two odd Turks.
At a certain point past midnight, our Mexican host had shared a link to Spotify’s new collaborative party playlist.
Previously called ‘group session’, this type of listening party was first introduced by Spotify in 2021, and transformed into ‘Spotify Jam’ in September 2023. I had missed this as I had moved away from Spotify in protest against Joe Rogan getting paid by Spotify to platform antivaxxers, but was instantly fascinated by this social function of the platform, as it creates a form of democratisation over the party playlist.
Joining a ‘Jam’ allows all guests to add to a playlist from their own devices that gets broadcast through a single speaker – the DJing-task was thus decentralized. The ‘jam’ function afforded a level of anonymity in the physical realm, since you had to open the Spotify app to know who picked a song, reducing the potential for ‘AUXiety’. When the host enables it, all users also get control over which song gets played next. This also means they can push songs down in the queue, end a song, or even delete the queue; a host of actions that were not attributable to specific users in the Jam. Since the playlist’s locus of action is decentralized to everyone’s mobile phone and accessible to all, the Jam can be democratising but also create a hidden struggle for control.
This new feature can therefore be a recipe for some good old norm conflict (which just so happens to be the topic of my PhD).
You must know, my Belgian friends can get very intense about music. They have a certain sensitivity for which songs should follow each other (the vibe shift needs to ‘work’) and make no qualms of putting their song first if they feel it fits the vibe better. They also have a tipping point for when to end a song; most songs should not be played entirely, (“4minutes is long!”) but we should at least hear the chorus. When we’re many wanting to play something, cutting a song short also offers space for more songs, so these actions are not frowned upon when there’s many DJ internets. I came to realize these are some pretty established norms among this friend group, yet they are not obvious to an out-group, especially when it is not clear who is doing what. In the past when the playlist and output device had a central location in the physical space, it was also obvious who to direct grievances to and sort out disagreement. With the Jam, these actions are obscured from the physical realm.
I had not been properly paying attention to the music, casually dropping in and out on the dancefloor, when I noticed a song was abruptly switched after 15 seconds. I asked what happened to one of my Belgian friends, whom I knew would be consumed by the playlist, and he complained that he doesn’t know who’s doing this – the queue had also disappeared a few times. He bitterly said he had a suspicion, pointing across the room. I casually went to confront our suspect, and after some chatting I found out our new Mexican friends had apparently been diligently putting their songs in the queue but kept getting other songs put above his, so theirs were never played. And when they finally were played, they felt it was cut short unfairly (“ALL 6 minutes deserve to be played!”). They weren’t really sure who was doing this, so getting frustrated, he and his friends had started skipping the songs that were put in front of his songs, almost culminating into a conflict on the dancefloor.
Queueing is a very culturally determined practice and I’ve seen norms clash over it so often – I still remember the desperate look on my Australian friend’s face after he had been trying to get a drink for half an hour at a busy Brussels bar. The later it gets, the more these queues devolve into a ‘work your elbows in the crowd till you touch the counter’ – type of ‘queue’.
It makes sense that there are also different normative practices around queueing songs, though there’s two elements that differ from physically waiting in line; queueing a song has an effect on more than just the person choosing the song – it’s a decision that affects the collective; and the platform architectures of Spotify’s Jam shape the visibility of queues differently than in the physical world, as the actions of skipping and changing the order are not attributable. This complicates communication on how to find a consensus among differing norms.
In the end my curiosity on our Spotify practices (and some welcome reflections by my Turkish partner) made me capable to broker peace between the different groups (I guess 2024 will not be the year where I stop meddling!). I explained to my Mexican friends that it wasn’t a case of malice, it was just a different norm, but that I understood how it feels unfair, and I told my Belgian friends what I had learned from my Mexican friends. At first my Belgian friend said that if they really wanted to play their songs, they should switch to their song when the time is right, but I pointed out that this “right” time is not obvious for people who have not partied with them before. They reconciled and admitted that there is perhaps a clash of norms, and we managed to continue partying together with a clearer communication over the shared playlist.
There were two more pieces worth mentioning on the social shaping of Spotify’s jam function; the role of digital literacy, and the possibility for capitalist stratification.
I noticed that some people did not fully understand how to add things to the queue, which led to some queues accidentally being wiped and songs skipped. Again, without visibility over such actions, malice was assumed and added on top of the frustration both sides felt. Hanlon’s razor is thus best applied to Spotify’s Jam! Some were off by a lot (as one can expect at a New Year’s eve party) with the hilarious incident of my not-very-sober friend who took the whole Spotify jam off the speakers to connect her phone, as she thought we were all just one by one connecting to the speakers. She abandoned her autocratic DJing after one song, so we took the jam back online.
We also noticed how easy it would be for Spotify to create inequality in the system. For a moment in the beginning we thought Spotify had made a tiered system where its premium users would have their songs appear at the top of the queue, but as the evening progressed this did not seem to be the case anymore. I can just imagine Spotify would not be peeved with its capitalist mindset to give more social power to their paid customers… For now Spotify seems to have resorted to an autocratic option (where the host can control the order and all other users can only add to the queue) or a fully democratic option, with the potential for chaos and norm conflict.
In any case, I had a fun evening, seems like I can’t ever fully let go of my PhD (go check out my paper on the shaping of social norms by platform architectures if you enjoyed this) but I guess by now we all know the answer to the question whether I’m “fun at parties” :’)
Photo by Point Normal on Unsplash
-
Cyberdiplomacy at the EU – insights and personal efforts

On January 30th 2021, I ended a 2,5 year adventure working in the European Union institutions. I spent this time at the EU Institute of Security Studies, the EUISS, where I worked on the EU Cyber Direct project, providing research support to the European External Actions Service in its cyberdiplomacy endeavours. I have decided to dedicate my full time on my PhD research at the Vrije Universiteit Brussels at IMEC-SMIT and the Brussels School of Governance, where I will be part-time affiliated with the Hannah-Arendt Institute. My doctoral research will focus on platform architectures, the organic spread of misinformation and online radicalisation and the ways platforms shape the agency users have to shape social norms around content sharing.
My time at the EU left me with many impressions and some accomplishments. At the start of the experience it felt like I had been living in Rome all these years and was suddenly summoned to work in Vatican City. The impressive architecture of institutional buildings in Brussels, which I had so often walked past as a Brussels citizen, now felt like cathedrals for democracy (and bureaucracy…). The centrality of Brussels in the European empire, even more epitomised by the inner Brussels bubble and hierarchies, its jargon and odd customs,… at times working for the EU felt similar to working for the Holy Roman Empire. These cynical feelings eventually subsided as I started understanding more about the inner workings of the greatest peace project (and experiment?) ever set up. I gained some respect for the work of the European Union, despite all its defects.
I spent my time at the EUISS providing research support for the EU’s cyberdiplomacy efforts. The EU has many diplomatic endeavours in connecting with countries in the digital landscape, one of them is cybersecurity focused. As every country in the world is navigating its way through the digital revolution, The EU deemed it important to understand how everyone perceives their route. Mass societal connection to the information highway brings many benefits, but also exposes society to many vulnerabilities that are hard to deal with. It’s no secret that some countries have been taking advantage of these vulnerabilities. There’s strategic benefits for these countries in exploiting the digital holes that are left behind while we’re all building digital infrastructure at a breakneck speed. I learned that the EU seems to want this global occurrence to be a collective endeavour where citizens protection online is the main priority (with protection very much interpreted from a liberal-democracy perspective).
Such a collective liberal-democratic strategy previously paid off after the European continent was ravaged by internal war. Cooperation works from the EU’s perspective. In the few years that I was working on the EU Cyber Direct project, I saw an EU trying to understand other countries and regions’ cybersecurity positions in order to adapt its cooperation ideas to the preferences of everyone participating in the global digital space. I saw how the EU and its member states have tried to broker conversations at the United Nations for peace and stability (often too careful in condemning allies) and support other countries in developing cybersecurity strategies.
A more cynical reading of these efforts is that the EU and other global powers prefer other countries to get ready for state-sponsored cyber operations. If countries know how to prevent devastating consequences and unintentional loss of human lives caused by cyberattacks, it will allow technologically advanced countries to wage cyberwar more efficiently. Though never acknowledged as one of the EU’s policy goals, the EU’s cybersecurity capacity building was probably not only coming from a perspective of peace and love for all citizens of the world.
While such a policy perspective is not one I endorse, I did salute the capacity building support and traveled around the world to speak about how the EU does its internal cybersecurity cooperation. Not to push a strategy for completely different regions in the world, but mainly to exchange best practices. Traveling for these conferences gave me new insights on how we think about security of the internet from different perspectives. I bundled these insights in 3 regional engagement mappings for the European External Action Services, one on Latin-America, from which I condensed my analysis of the region’s balancing act in a blog post for the Elcano Institute, one on Africa, and one on Southeast Asia. There is no right or wrong way to do cybersecurity in the end, every country and region approaches cybersecurity cooperation and awareness in ways that work for their region.
During my time working with the EU Cyber Direct project, we connected hundreds of experts, academics and digital rights activists to EU policymakers, putting them in the same room to exchange perspectives. The COVID-19 pandemic made that aspect harder, and working on cyberdiplomacy really made me understand the value of human-to-human contact. I mentioned this importance in my opening statement that I was honoured to make at the 2019 UN multistakeholder intersessional of the Open Ended Working Group (OEWG) on Developments in the Field of ICTs in the Context of International Security. I wrote about what these UN meetings are about for a Belgian audience to create more awareness on the importance of this process.
In the UN statement I made an analogy of human interaction to the DNS system. Human networks are connected through routing points, similar to computers. These human routing points have a role to play in connecting everyone in their directory to other parts of the world. This is for me what multistakeholderism is about. It is important that the people who are routing points in their local and regional communities are involved in such global processes on securing the internet. Their presence at fora like the OEWG is key to making sure a broad variety of actors has a say in the security and stability of the internet, so a robust human DNS must be built between them.
The point I wanted to make in that statement, was the need to get a variety of actors involved in the cyberdiplomacy conversation. I supported the European Security and Defense College in the creation of an e-learning module on cyberdiplomacy to demystify the concept and processes for European diplomats. The e-learning is openly accessible to anyone, as the understanding of cyberdiplomacy should stretch far beyond diplomats representing their states interest.
My time at the EUISS was not exclusively spent on cyberdiplomacy and the EU Cyber Direct project. I was grateful to also be able to contribute to the institute’s strategic foresight efforts. These allowed me to develop my insights on the security threats that stem from social media, which are not a topic of debate in cyberdiplomacy. This is also why I decided to pursue this topic further in a dedicated PhD research project.
There are good reasons to keep social media, misinformation and other content issues out of security debates, which are at the centre of cyberdiplomacy. For one, it remains problematic to securitize content, and it plays in the hands of global actors who would prefer to gain greater sovereign control over information that circulates within their borders and reaches their citizens. It does however also negate the fact that there are security threats stemming from content that circulates on the internet. On January 6th 2021, a mix of extremists, Trump supporters and conspiracists stormed the US capitol building, supposedly to ‘take back the steal’ and protest the election loss of Donald Trump. Five people died in this riot. One year earlier, we predicted a scenario of civil unrest in the US fuelled by online misinformation and extremists organising in online groups. Our scenario was supposed to take place in 2024, but perhaps the global pandemic fermented many underlying rotting issues and stank up the place faster than I expected.
Calling the January 6th incident the start of a civil war is hyperbolic, but it was symptomatic to the very real security issue stemming from the social web. The artificial wall held up in the international discussion between harmful code – harmful content also leaves a vacuum for those countries that are dealing with the growing pains of societal digital connection. There are many countries seeing the waves of instability stemming from the internet, but see no clear solution to avoid it from turning into conflict. Without global discussions on this issue, countries cannot support each other in finding viable, human rights-respecting solutions to this problem. This vacuum is easily filled by actors supporting more online repression and surveillance to guarantee stability. If I had more time and space at the EUISS, I would have still written a Brief about the need for global capacity building and best practice exchanges on dealing with disinformation in a rights-and-rules-respecting way. The EU and other countries making policy decisions however haven’t found the best approach themselves. There needs to be more evidence-based policy making first. Countries around the world need to experiment with rights-respecting interventions, acquire evidence together, adapt to local contexts and investigate the effectiveness and impact of certain platform regulations and interventions.
These issues of misinformation and online hatred fester all around the world on social platforms that are ran by companies that seem unbound by any national legislation, and unbothered by their societal responsibility or lack of democratic input. In my view, most of these platforms are inherently problematic because of the business model and architectures that guide their social interactions. That is why, as part of the What If series, I wrote out my utopian ideal of a social media platform in 2024 where users could get their news as well as engage socially.
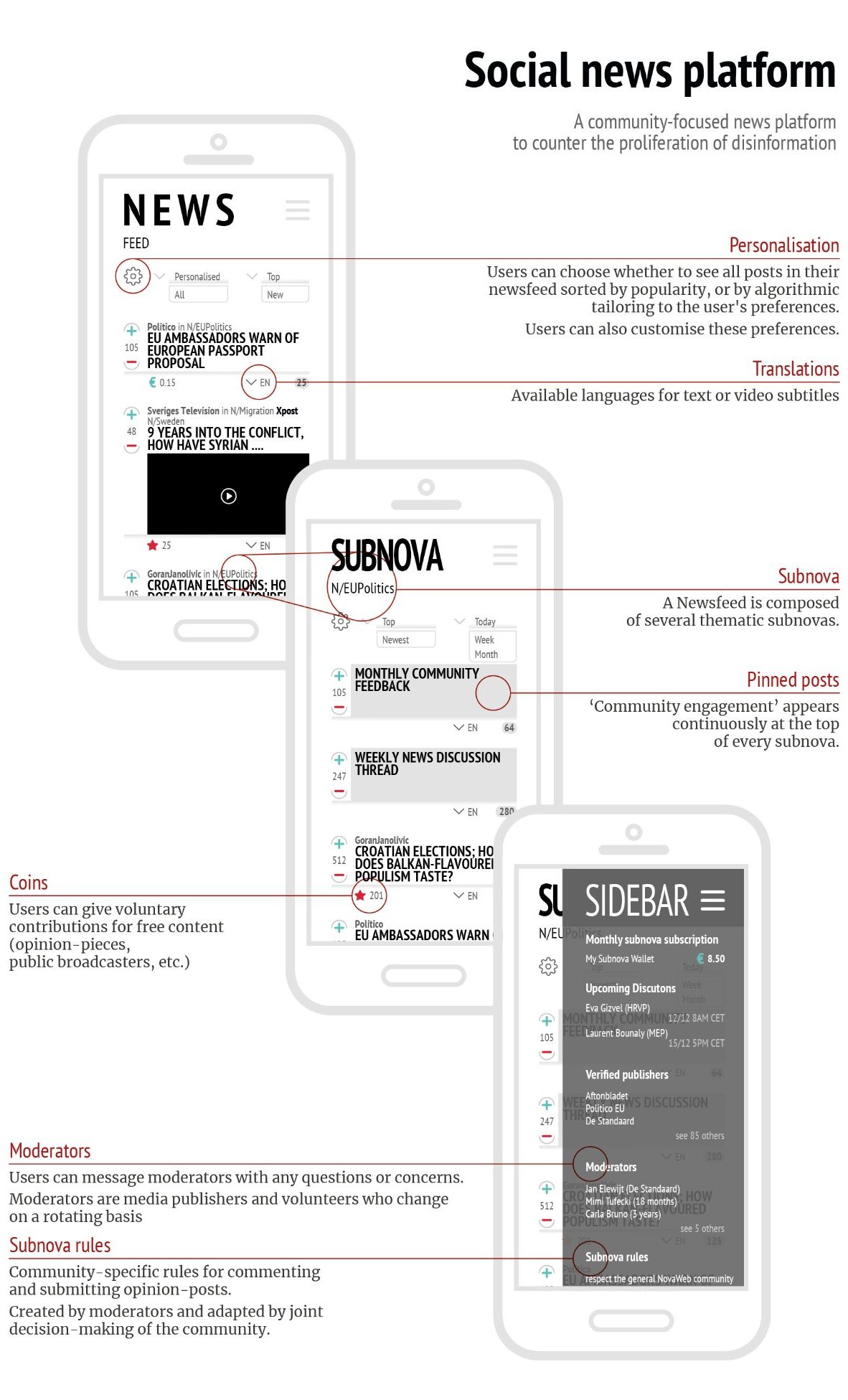
The key importance of such an interest-based social platform are: trained moderators who are part of the community, understand the norms, context and tone and can be held accountable by their community; and a subscription/wallet based monetization.
I see many challenges ahead for the open internet, as geopolitical interests are seeping into internet governance issues increasingly more often. One such example was the discussion on a potential ban of the Chinese social media app TikTok. I wrote a piece on our Directionsblog how the concerns with TikTok are framed as cybersecurity concerns, but they are actually more a matter of national security where states such as the US don’t want data of their citizens to fall into the hands of a country like China. If states truly want to tackle the security problems with platforms like TikTok, the solution is not to ban the platform and harm user rights that have formed communities on these platforms. The solution is to create a rights-and-rules based social media, for ALL social media platforms.
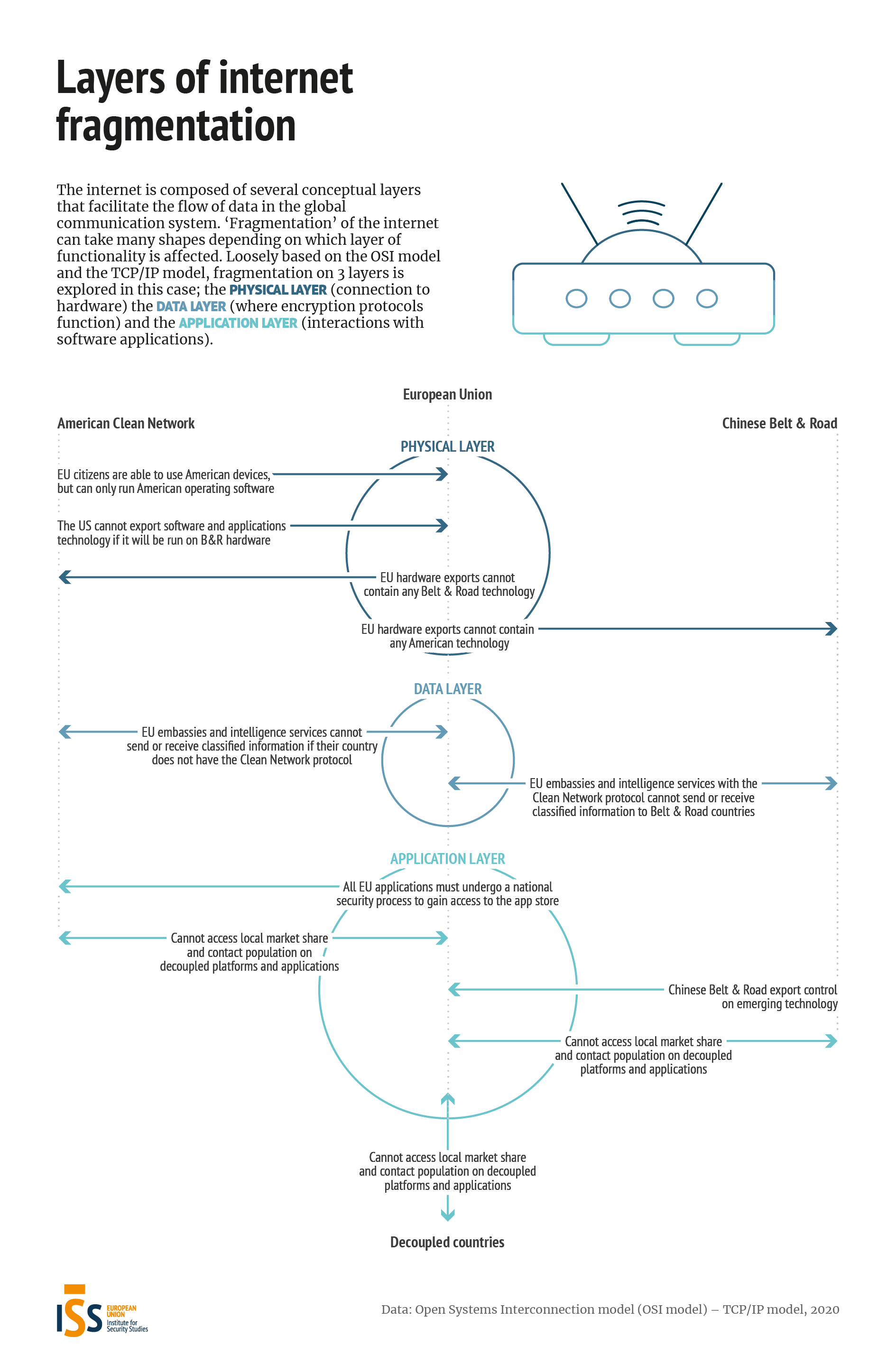
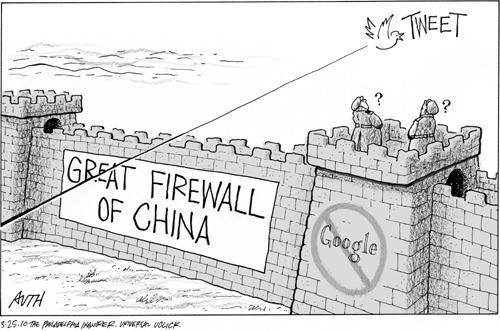
When the mindset of a free and open internet starts taking a backseat in security discussions, the internet will start fragmenting on several layers. A lot has been written about how the internet will not fragment, especially on the DNS layer, but geopolitics can intervene in several other layers of the internet. For the last What If scenario that I made at the EUISS, I hypothesized what a fragmented internet would really look like on a Physical, Data and Application layers of the internet (loosely based on OSI & TCP/IP model).
The global network of information has always been balancing between decentralisation and centralisation. As the balance seems to be tipping more to decentralisation, it is important to keep regions from fragmenting their internet space and cutting off or inhibiting the flows of communication.
The EU can have an important role to play in stimulating cooperation towards protecting a rule-based free and open internet. I look forward to keep working towards these goals in the future, possibly with the European Institutions but always with a sharp and critical eye on the Union.
-
How the Russians really hacked the 2016 election

The Russians tried to hack the American elections. But not in the way that we’re used to. This piece treats some possible consequences for the West of the information war Russia has taken outside of its borders.
Piece previously appeared on De Morgen on 16/12/2016
In a disconcerting long-read of the New York Times we see all the staggering mistakes made by the Americans so that the Russians could carry out strategic hacks in the run-up to the elections.
Both for hacking the Democratic National Committee and hacking the emails of Clinton’s advisors, there is clear evidence of Russian interference. The Russian state hacker groups Cozy Bear & Fancy Bear, also known as APT28 and APT 29, were recognized in the forensic investigation. The self-proclaimed “lone wolf” Guccifer2.0 who allegedly had committed the hack alone, also made some stupid mistakes making it clear that this was a cover-up of Russia.
Russia’s Information War
The tactics used by Russia here come straight from their information war handbook.
In an information war, information is used for psychological purposes. The goals is to confuse the population with erroneous information and causing unrest with leaked information. The confidence in the traditional sources of information drops and facts can no longer be distinguished from fiction.
The internet is a godsend for this type of warfare, and Russia is perfecting these type of operations.
During the elections in Ukraine and the subsequent annexation of the Crimea in 2014, their use of information operations peaked. They made strategic leaks to discredit the pro-European presidential candidate while distributed fake photographs about Ukrainian soldiers and spreading disinformation (the website Russia Lies collects many of the disinformation campaign on Ukrain)
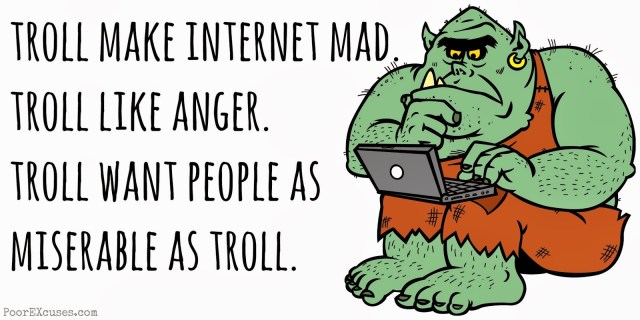
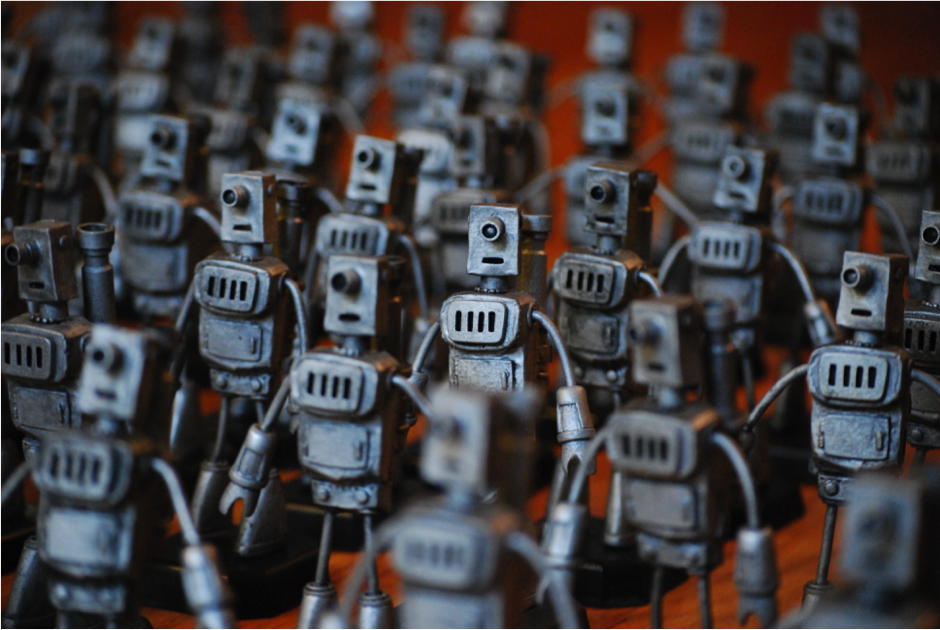
Russia is also known for spamming internet forums with their Russian web brigades. The Russians have a veritable troll-army whose daily task consists of posting thousands of pro-Russian comments on the web.
Sounds familiar in the run up to the 2016 election?
harmful code vs harmful content
The CIA had already openly accused Russia of these tactics, but the American intelligence community was first putting its effort in an investigation on hacked voting computers.
In the run-up to the elections, it emerged that there were many vulnerabilities in the outdated voting computers. The day before the elections, for example, security company Cyclane showed that it is possible to change the names in a voting computer if you have physical access to them.
Investigating whether the systems had been hacked was a stop-gap measure to restore confidence in democracy and elections. If it could be proven it had not, then maybe the people could trust the election? Sowing uncertainty about the election systems was also part of the information war; making people doubt the results of the election. Such uncertainty is a different way of ‘hacking’ the system, and one that would have definitely had its effect had Trump not won (his voters would have most likely questioned the results ).
The Russians did not have to hack into voting computers to reach their objective, the main goal was always to falter the confidence in democracy, not necessarily to get a puppet like Trump elected.
The US is struggling to recognize that it has a problem of information security.
This has nothing to do with America’s arrogance, but above all with a fundamentally different view of international digital security. The Western doctrine of cybersecurity revolves around protecting (digital) systems, and the information contained in them. Information is no more than a series of zeros and ones.
While the West is only mindful of ‘malicious code’, Russia sees’ malicious content’ as a weapon as well. The psychological weapon of “information operations” as described earlier. It is no coincidence that the Russians prefer to talk about information security instead of cybersecurity. (note: the infosec community also talks about information security, only this term was politicized when explicit demand came for the UNGGE to be called the UN Group of Governmental Experts on Information Security) Influential information is dangerous in Russia’s eyes, and it is not even necessariy to attack any digital systems.
Putin is known for blocking opposition websites and bloggers and actively disseminating lies. A list of lies on the European Union is also kept up to date in the Disinformation Review, a magazine recently set up by a task force of the EU.
It should be no surprise that this vision is share by other authoritarian state like China, Iran, Turkey, where control of information is vital to streamline political preference and keep dissident voices in check.
It seems that Russia’s use of an information operation was not only a way of testing the potency, but also to warn the West of the ‘danger’ of a free and open internet.
A free and open internet: the achillesheel of the West
Now that Putin is also executing his information war abroad; the West has a problem. Freedom of expression is a core value in an open and free society. Unfortunately, this is also the Achilles heel of the West, and the Russians have made good use of it. Not even a long time ago, WikiLeaks was the epitome of free information gathering, holding those in power accountable. In recent months, by distributing only information extracted from Russian hackers, Assange became an indirect spokesperson for Putin.
Trump does not owe his presidency to Putin. There has been some rumbling in America’s lower abdomen for some time. But in the toxic breeding ground of filter bubbles and a post-truth society, there is an opportunity to expand Putin’s sphere of influence. Now that American confidence in democracy has fallen to a low point, the US seems ripe to join the authoritarian states.
The Democrats know that Putin played the game like that. But if they admit that there is a problem with the free flow of information (whether or not such operations have an impact), they might also want to exercise control over all information. One might think they can only beat the Russians in the information war by putting a tighter control on the information in their own country. Following the Reflexive Control Theory, this would be exactly what Putin wants.
The West is already slowly moving in that direction. Counternarratives against radicalisation, restricting hate speech and banning fake news. And how can you be opposed to it, when you see what kind of conspiracy theories are currently finding a platform?
All the signs indicate that we will only go one way: that of a more controlled Internet. With someone like Trump at the wheel, it is not impossible that this control in “the land of the free” will go much further than stopping Russian influence.
The question on my mind is what direction my native Europe will take. Are there means of arming us against the next information war without having to give up our online freedoms?
I do not believe in it, but I sincerely hope that I am wrong.
-
The IoT Zombie army is knocking on our door, what are we going to do about this?
(this article previously appeared on Knack-Datanews)
October 21, the world is confronted with an unprecedented DDoS attack, mostly caused by insecured Internet of Things devices. IoT manufacturers were put under scrutiny, and we were all given a sneak peek of the consequences when we don’t include including Security by Design. Where do we go from here?
The facts: on October 21 a Distributed Denial of Service (DDoS) attack on the DNS provider Dyn caused disturbances on the internet. Dyn is the equivalent of the internet Yellow Pages; they direct you to the right IP address when you type in the URL of a website. DDoS’ing them is therefore a simple, but effective way of making a large quantity of websites inaccessible. No Netflix and Chill, no Reddit, no Twitter. In short, people had to go outside and be productive.
DDoS attacks are as old as the internet itself. When a server is flooded with requests, it cannot reply to other legitimate requests. This happens sometimes when a site becomes unexpectedly popular and has a surge of visitors, but a malicious DDoS attack usually uses infected computers to spike the visitor requests.
A lot of organisations have tried to instill measures to mitigate DDoS attacks, yet this incident was remarkable because of its size. Dyn reported that more than 10 million IP addresses were involved, the equivalent of 1,5 Terrabye per second.
It was discovered that this was mostly possible because of the festering supply of vulnerable internet of things appliances.
Internet of shit
The security community has been cursing for a while now about the Internet of Things, often scorned as the #InternetOfShit. These are all the appliances and gadgets that can (often needlessly) connect to the internet, like your tv, security camera, fridge, but also your car, your toaster, your lightbulbs, your doorlock, and even your bottle of wine. It is estimated that in 2016 about 6 billion appliances are connected to the internet. A dizzying number.

When more appliances are connected to the internet, there are more vectors to infect, which contribute to computing power for attacks.
This was also known by the creators of the Mirai virus, which purposefully infected IoT devices. Millions of infected IoT appliances were thus added to a botnet, creating a monster army of zombies that were used for DDoS attacks, unbeknownst to their owners.
Zombie hideout
A logical step if we want to prevent such attacks in the future, is cleaning up those devices. A lot of users know by now that they need to install antivirus software on their computers, but are not aware that their television or security camera can also be infected and participate in attacks. There is very little motivation for users to do something about this, since the impact of the infection is nearly unnoticeable in daily use.
Every country thus has the responsibility to notify users that show up in the IP logs of recurring DDoS attacks. They can inform the general public, generate awareness, and use certain incentives to secure IoT devices. This way, the zombies can be deactivated and botness can lose their strength.
An IoT that deserves our trust
Unfortunately users cannot do much themselves if they are not even capable of securing their devices. It appeared that Xiongmai, a Chinese producer whose devices was omnipresent in the attack on Dyn, had set default passwords on its devices, that couldn’t even be modified.
This was apparently the case with all devices sold before 2015. This kind of vulnerability is sadly recurrent in many devices. If the password cannot be modified, it most definitely can be controlled by someone else.
Producers are still free to choose how much security they want to install. There is no international security norm for connected devices. Since a cyber-secure connected toaster isn’t exactly a big selling point, this step is often skipped to cut costs.

It is therefore important to call IoT producers to account, force them to have minimum security standards, and penalise those that don’t.
Organisation like the Internet of Things Security Foundation, and volunteers of the security collective I Am The Cavalry are taking matters into their own hands by setting up security frameworks. The latter even managed to make the producers of medical devices swear a hippocratic oath to no longer sell devices that do not have built in security.
The EU is also developing a proposition to force companies to abide to certain security standards, and to find a labelling system for secure IoT devices.
While its certainly useful to secure European production, it lacks some impact in a globalised world. If producers are prohibited to use cheap Chinese components when they don’t abide to those standards, it will be hard to stay competitive. If there’s little knowledge of the issue, few consumers will pay more for a “secured” IoT device.
We need international rules, although it’s not bad to start with a European label.
Too little, too late
When IoT devices didn’t have proper built-in security settings, it’s difficult to secure them afterwards. It’s commendable (and necessary!) that we try to force security by design right now, but it’s actually too late already.
The IoT craze has started a while ago already, and many appliances were sold that can’t install patches remotely. Often users must make a manual firmware update, or even hand in their appliance. Since the lifespan of many of those devices, which are often household appliances, are often only replaced after 5 to 10 years but its users, it’s quite possible we’ll still be living for a while with the consequences of the IoT zombie army.
it’s very pessimistic to say, but this is only the beginning.
-
Is our “Digibesitas” giving us Technophobia?

(This article previously appeared in Dutch on Knack – Datanews)
The tendency to curse smartphones isn’t new. But I am becoming fed up with the articles, cartoons and art that are going for the low hanging fruit of bashing new media technology.
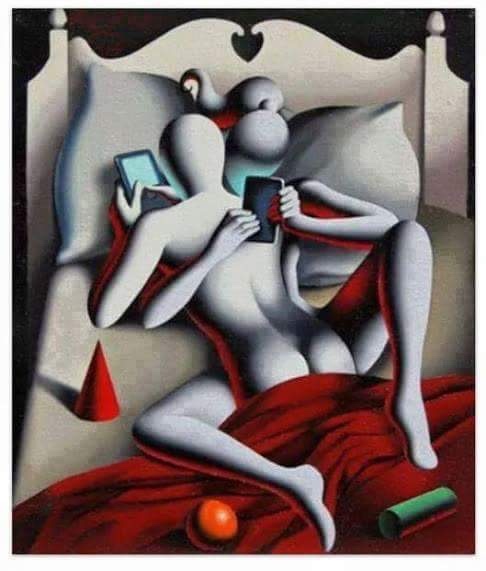
From criticizing the display of personal life on social media and fishing for likes,
to the insensitivity of the “sharing culture”
to being chained to your computer and smartphone
There are too many “wake up Sheeple” cries in popular culture these days, blaming hyperconnectivity to cause society to be anti-social, attention seeking and narcissistic.

I’m showing a bunch of examples in this post that I’ve been collecting for a few months, since they irk me. Like the well-intentioned, but very cringy Spoken Word artist below, who rhymes about how iPhones makes us only think of the “I”.
Even Zenpencils, who I really respected, compares social media to a Heroin Addiction.
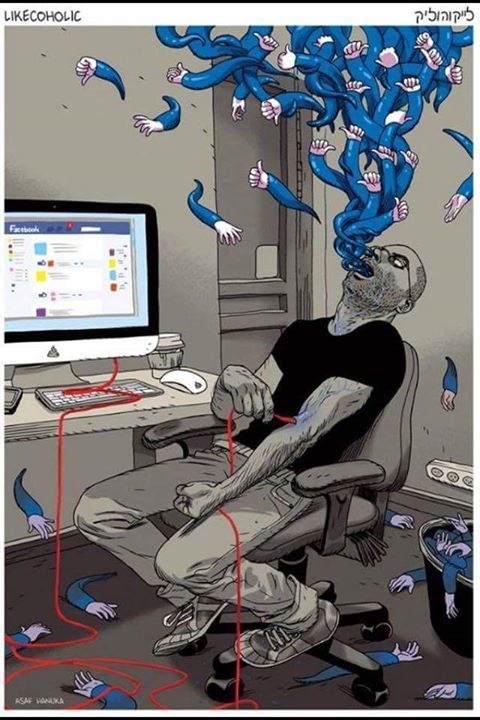
(and here’s another such comparison… not so original eh?)
But also more serious voices are riding the wave, like the TED-talk of Sherry Turkle, who is convinced that the virtual connections only make us more lonely.
The Belgian research institution iMinds even came up with a name for the “overconsumption of digital media”: Digibesitas.
It’s starting to feel like Neo-luddism, the Unabomber’s ideology against a new industrial technological society, is back in a softer form. There’s no computer stores being bombed, instead hyperbolic cries try to convince us how society is ill because we’re spending a bigger part of our social activities online.
Kranzberg’s 1st law says “Technology is neither good nor bad; nor is it neutral”. It all depends how it is being used.
“we should all throw away our smartphones maaaaaan, we’re so disconnected”
(I once heard someone say at a dinner-party, that was entirely arranged through a facebook event.)
It would be naive to argue that our social interaction hasn’t changed. Au contraire, the digital revolutions has caused quite some earthquakes, moving all our communication to the digital spectre. As I previously wrote, our memory is even changing due to the possibility of digital storage. It would also be blind not to recognise that there isn’t a sizeable portion of fhe population addicted to social media. There have been countless reports on how algorithms are affecting and steering our behaviour.
But there are also plenty of people who still have a healthy relationship with social media. This pathologizing social media seems to only give one alternative: throw it away.
Some nuance is due on the impact this digital transformation has had on our communication, since there have been plenty of positive aspects of the digital social life.
Digitally enhanced life
Thanks to the sharing culture, we’ve got an incredible archive of testimonies during historic occassions, like the footage during the Paris attacks, the detailed accounts of the refugee crisis, … but also on an individual level, your entire family can easily watch and re-watch the first words of a new addition to the family, or you can watch and re-watch your GoPro filmed escape from a bear that suddenly surprised you in the woods,…
And let’s not forgot movements that were mostly gained momentum through social media such as the Arab Spring or #blacklivesmatter.
Digital communication has made it possible to work from home and take care of your children or a sick family member. There are even so many more possibilities arising to keep doing the same job from the other side of the world, an evolution welcomed by the growing population of tech nomads.
People can stay in touch with friends from all over the world, you can become friends, or even become part of an entire community of people that you’ve never met before. The internet offers an inside look on other cultures for those who cannot afford an expensive airplane ticket.
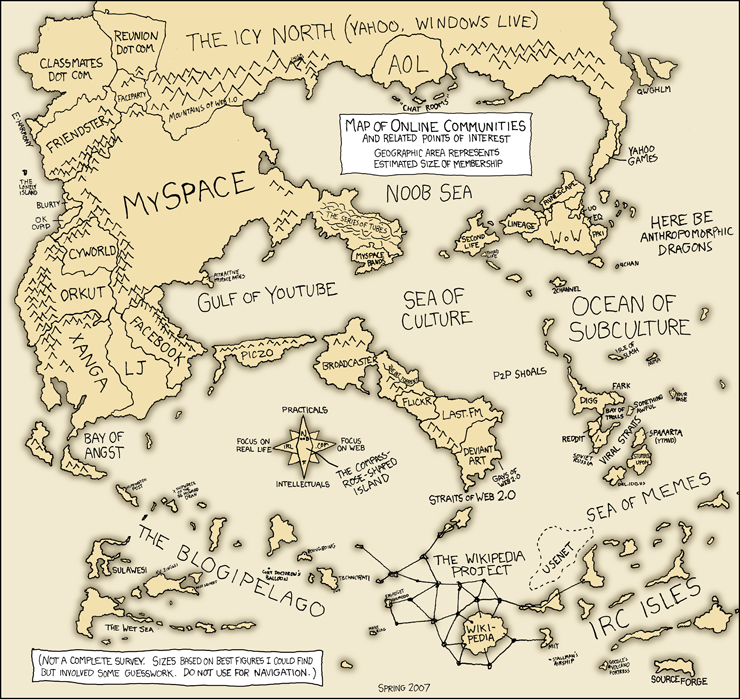
(online communities 10 years ago, in 2006)
Not only has the digital life had a major positive impact on our social life, not taking it seriously can even be harmful.
As Julianne Ross wrote in Wired, the online life is just as real for many as the Physical world. Emotions people have online are just as real as the ones they have offline. Suggesting that it is not, means people aren’t taken seriously in cases of cyberbullying or sextortion.
These are very real problems, that can have an enormous impact on the human psyche.
The biggest problem with the digital society in my opinion isn’t that people are staring too much at screens, but that society hasn’t accepted yet that we are all real people online, with real feelings. Not acting like it can have real consequences (Hong Kong has even noticed a peak in suicides because of cyberbullying). Maybe the presumption that kinds are becoming more narcissistic is because they forgot that every ‘like’ comes from an actual human, and they should cherish it.

The core of my rant is this;
Technology changes, but humans are still human, in digital form.
Anti-social people will just use the tools to stay anti-social and ignore you, possibly retreat to another world.
Young people will always crave attention and validation.
Narcissistic people will always feel like nobody likes them enough, no matter how many hearts you throw at them.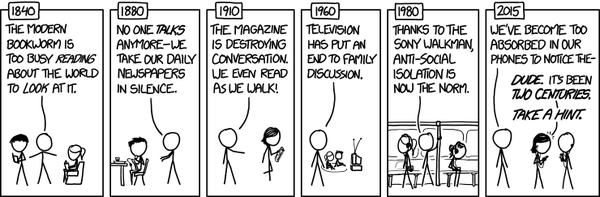
The Digital society has only given us new tools. Tools we use royally, that facilitate and enrich our lives. We still create society ourselves. If this means we’re retrieving more into a filter bubble, it’s maybe becauae the tools give us the possibility to follow our human nature to finding connection. What SHOULD be more central to the conversation is the need for tools that break through bubbles, tools that facilitate discovery. But that is a whole other conversation on how we should reimagine platforms.
In short: yes, the digital life impacts our social interactions. But that doesn’t make them less real.
-
Digital Amnesia

(This article appeared earlier on Vice: The Motherboard NL)
With all this talk about ‘digibesitas’, let’s add one more new-society disease to our vocabulary: Digital amnesia. It’s the act of forgetting certain things when you store them on you digital devices.
I started to notice that my memory is failing me lately, and it’s was really beginning to frustrate me.
Remembering the street that I had just looked up, or the name of that movie, with that actress, you know, who was together with that guy, but I can’t remember any of them… It seemed I had to rack my brain much more to remember the stupidest things, and I couldn’t limit myself to less than 10 internet searches a day for these stupid kind of things.
Early onset Alzheimer
When I couldn’t even remember the pin code of our shared food-account at the
 supermarket counter at rush hour, and had to look it up in the notes of my phone cause I knew I had put it there temporarily ‘just in case’, I went to the doctor.
supermarket counter at rush hour, and had to look it up in the notes of my phone cause I knew I had put it there temporarily ‘just in case’, I went to the doctor.I dead-seriously asked him if Alzheimer is possible at my age and he looked at me and said “Nathalie, go to sleep earlier”.
If he wouldn’t take me seriously, the internet would, so what did I find on one of my nightly internet-rounds? That we’re all collectively kind of worried about our memory.
Scottish researchers diagnosed this memory loss a few years ago as the ‘Busy Lifestyle Syndrome’. According to their theory, our capability to remember isn’t decreasing, but we just have far too much to remember these days. Therefore some recollections disappear in the realms of our brain, buried by the avalanche of information.This is only half the truth. In order to cope with all this information piling up on us, we try to save a lot externally. Our smartphone has become our biggest ally, but it also adversely seems to be the cause of our memory loss.
A recent study initiated by the cybersecurity company Kaspersky Lab speaks of ‘digital amnesia’. This entails the phenomenon where you will start forgetting information after you’ve entrusted it to your digital device.
Your brain will stop putting in an effort to remember certain bits of information, since it knows those are being remembered somewhere else.
The only knowledge it still retains is the instructions where to find said information.
Your brain becomes a directory to where certain files can be found on your smartphone/computer/the internet.As if you’re asking your brain “hey buddy, can you tell me where Ann lives again?” and your brain is this lazy slob lying on the couch watching tv, yelling “she mentioned it somewhere in this facebookconversation you had a while ago. Try searching with keywords ‘party’”
According to the Kaspersky study, more than half of its respondents will think of keywords to Google the answer, instead of thinking of what the answer might be. This is also called ‘the Google effect’.
The joy of forgetting?
Our cognitive processes are truly changing when the internet and smartphones are within arm’s reach, it seems. According to Maria Wimber of Birmingham University, these devices allow our brain to ‘selectively forget’ the externally saved information to make room. Forgetting is quite healthy for our brain, and when we save that info on an ‘external brain’, we feel safe and assured that forgetting won’t mean that info will be lost. We can now make space in our head’s hard drive and process more new information.
So far the good news.
Because what if you suddenly don’t have your external brain with you? What if you need some important information that you hadn’t remembered because you counted on that smartphone?
Your data running out when you still needed to look up the route to your friend’s house.
 Missing your last bus when your phone has died, and not remembering a single phone number from the top of your head to help you out.
Missing your last bus when your phone has died, and not remembering a single phone number from the top of your head to help you out.Not remembering the name of that grey white man that is walking enthusiastically towards you at a conference, and you can’t quickly check your linkedin.
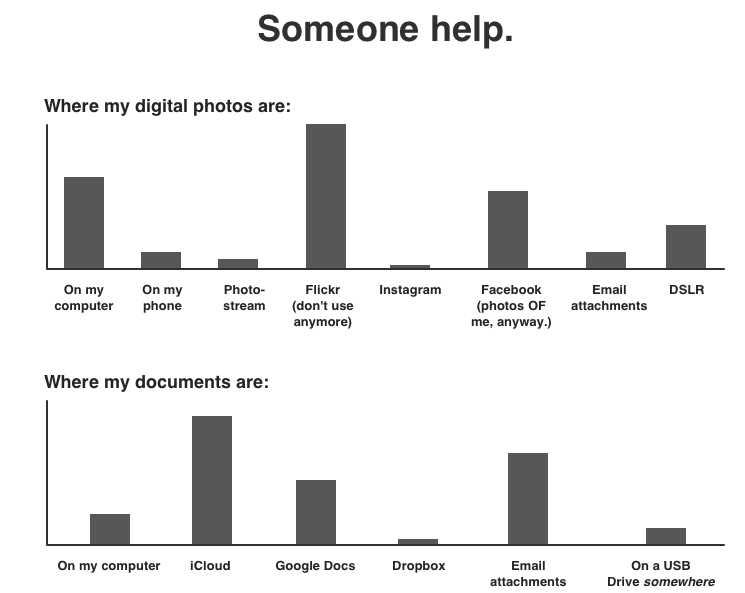
Or even worse, when your brain accidentally deleted the directory to some information because there’s too many storage spaces. That article I was going to reference to, did I save it in my bookmarks? Did I put it in my Evernote? Did I e-mail it to myself? What keywords can I use to google it and find it again…
(Courtesy of Doghouse Diaries)When the external brain disappears…
We unknowingly put so much trust in our devices because they are so efficient and user friendly. It almost makes us forget that they can disappear in a single moment.
You can lose your device, but also your back-up can disappear.
Whether it’s mechanical failure or magnetic field breakdown, back-ups on hard drive will not live forever. You will need to refresh them at least once every 3 years to make sure the data stays safe. After some more years, some of the files on your hard drive might also become unreadable because of ‘bit rot‘. Vint Cerf, the ‘father of the internet’ warned us for this phenomenon. Some files are only readable by certain programs, and those would no longer be supported by newer computers. You would still have the file, but no way to open it. (This colourful mess is all you’ll be left with)
(This colourful mess is all you’ll be left with)And the internet itself is disappearing and forgetting all the time to make space.
I recently made the painful discovery that my unused Hotmail-account, my very first e-mail address that I had created when I was 12, was completely empty.
Microsoft had made a big sweep of inactive accounts to create more serverspace and clean up its data storage.
Gone were my stupid but funny teenage e-mail chains with friends. Gone were my very first digital love letters with crushes. Gone was all this information that I will never retrieve again.This happens all the time, since the rapid growth of the internet also means an ever expanding amount of information that occupies server space and overwrites other data. Who knows what part of the internet will stand the test of time.
If we’re not careful, it is quite possible our collective digital legacy could go up in smoke in less than 50 years. It’s one of the reasons I donate to the Internet archive and its waybackmachine. Webpages disappear all the time when their owners stop caring about them.
One can say we’re at a point of no return, the internet and our devices have become an extension piece to our brain. We can embrace it, continue processing new information and rely on our external devices to remember it. And accept it might one day be lost.
We can try to fight it and try to remember everything to the point that it drives us mad. Print out all pictures and documents to keep in a box in the attic. Make 6 back-ups and store them a tin jar to protect them from solar flares and spread them over the globe.
But it doesn’t matter what kind of wonder pills you’ll try to take. One day we’ll all forget, and be forgotten.
-
How the Sony hacks made the US go into a cyber war frenzy

How the Sony hacks made the US go into a cyber war frenzy
Is this really how we’ll deal with cyberattacks in the future?
(this article was previously published in Dutch on Datanews)
Whether the Interview is a good movie or not is debatable, but we can all agree that it has caused a lot of commotion. Not only did it enjoy the weirdest marketing campaign in movie history and caused a diplomatic riot, it also set some special precedents, making many think the Cyberwar has commenced.
The events unfolding in the past few months could have been a movie on its own. Two comics make a silly movie about assassinating the current North-Korean dictator. The actual North-Korean leader is offended. Coincidentally the film production house is met with a heavy cyber attack destroying their entire systems. Theatres are threatened to “not forget” 9/11 in case they would play the movie. The theatres and production companies cowardly withdraw, which is met with a public outcry, and the film is released anyway with alternative means. The FBI is quick to point the finger to North-Korea, sanctions the country, while the North-Korean internet ‘coincidentally’ also goes offline. Obama is called a monkey, and in between people start remembering both country also have nuclear weapons.
We’ll have to wait for the DVD-release and the next Wikileaks to see the behind-the-scenes footage, but for now it has all been very amusing.
While the dust is settling, it’s interesting to have a closer look at what the Interview and the ‘Sony Hack’ has set in motion.
Playing the blame game with North-Korea
In the entire analysis of the Sony Hack, the diplomatic aspect is the most striking.
Already after a few days the FBI concluded the cyberattack and the threats made could be attributed to North-Korea, based on flimsy evidence.
A lot of doubt has been cast on this attribution by several experts.While the FBI refuses to admit how exactly the trail of its investigation leads to North-Korea, most of the evidence it gives or would credibly be able to give, is indirect circumstantial evidence according to experts.
While one would hope the US wouldn’t make such harsh accusations without a solid backing, we mustn’t forget the assumed Weapons of Mass Destruction in Iraq. Back then the US was also very sure of what later proved to be false accusations.
North-Korea denied the responsibility for the attack, but the New York Times saw a half confession in North-Korea’s statement that the attacks were ‘righteous deed of supporters and sympathizers’.
Was North-Korea aware these attacks were being launched? And is a country also responsible when it sees evil being done and doesn’t try to stop it?
The US turned down North-Korea’s offer to launch a joint investigation, and went in the offence. The 2nd of January it raised sanctions on the most heavily sanctioned country in the world. This was a world first, effectively being the first time the US punished a country for a cyber attack on an American company.
Very ‘coincidentally’ the North-Korean internet also went offline.
The US denied any role, although fingers can also be pointed to a country with suspicious motives. Such actions would be giving North-Korea just as much right to strike back covertly.North-Korea currently only responded furiously, with press releases like “U.S. Urged to Honestly Apologize to Mankind for Its Evil Doing before Groundlessly Pulling up Others”.
Whether the US has proof or not, according to Allan Friedman, researcher at the George Washington University’s Cyber Security Policy Research Institute, it is a smart diplomatic strategy to be overconfident in assigning blame for the cyber attacks. To prevent precedents from being made, it’s best to discourage other states from engaging in similar behaviour by punishing North-Korea, even when lacking concrete proof.
Is this the beginning of a Cyber War?
A lot of talk in popular media mentions cyberwar when referring to the Sony hacks, but was the crippling of a company really an act of war?
This lack of certainty on attribution is already vital to define this attack as an act of war. It is almost impossible to speak of a cyberwar in such a covert domain since wars are traditionally only fought between nations.
But let’s assume for the sake of the argument the FBI is right and North-Korea was behind the hacks.
When treating the term ‘war’ literally, we have to look at whether this was a use of force, as described in the United Nations Charter. It’s forbidden to use force, unless when used in self-defense, or when permitted through a UN Security Council resolution. If you don’t have that justification, you might have started a war.
Based on a lot of discussions and precedents, it has sort or less been agreed what such a forbidden use of force can be; inflicting harm with such a scope, duration and intensity that it threatens the territorial integrity or political independence of a state.
So when a lot of people die, and the national security is threatened, it’s a use of force. Makes you think twice about the impact of crippling a company that, according to Dr. Evil in Saturday Night Live ‘hasn’t been relevant since the Walkman’.But even here, when it comes to war, the cyber domain is a grey zone. A difficult domain where no clear lines can be drawn about what is enough ‘damage’ to regard something an act of war. There’s no international legislation, there are no precedents and thus there are no norms telling us when we feel enough damage is done for something to be classified a use of force.
Something Pentagon Press Secretary Rear Adm. John Kirby also repeated, with the plea to urgently set up international rules.A lack of such international legislation and precedents also means a country can attack another, and a country like the US can reply at will. Its permissibility depends on whether the international community condemns such actions or not, shaping the norms as a consequence.
But it would also mean this would be where the line is drawn for future reference. The US knows better not to turn these hacks into the great ‘cyber Pearl Harbour’. As cyberwar expert Peter Singer said on the Motherboard, ‘we’re not going to war with North-Korea because Angelina Jolie is angry at some Sony Executive’.
At the same time the US is taking the matter very seriously, treating the hack on American soil as a matter of national interest.
Especially after threats were also made.
Cyberterrorisme?
“The World will be full of fear. Remember the 11th of September 2001. We recommend you to keep yourself distant from the places [where the movie is shown] at that time.”
The threats made by the hackerscollective responsible for the Sony Hacks apparently left a great impression that made many speak of ‘Cyberterrorism’.
The term terrorism is used frequent to describe any threat without a clear state actor, solving the attribution conundrum. The concept of the ‘war on terror’ is still a controversial way to circumvent the traditional paradigm of “wars are only fought between nations”. The reminder of the US’ collective trauma made the nation immediately up in arms.
Sony added fuel to the fire by caving, and allowing the film to be withdrawn from 180.000 theatres. Allowing fear to rule and complying with threats is how to ‘let the terrorists win’. As Peter Singer also said, the way Sony handled the entire ordeal has turned into a case study on how NOT to respond to terrorist threats. Especially when these hackers have not shown any capability to carry out anything remotely physically damaging.
Such scaremongering comes with ignorance on what damage cyber attacks can actually cause.
Did Sony have the right to panic?
Coming back to the use of force, there has thus far not been an overt cyber attack that could be classified as an act of war, even though the possibility exists. With the Aurora Project the US even proved how much physical damage a cyber attack can cause.
The damage done to Sony was nowhere near comparable to such physical damage.
100 Terabyte worth of data was stolen, as well as ‘wiper malware’ was used. This type of malware destroyed Sony’s internal systems (from production planning to human resources). This meant the company has to replace all their systems, paralyzing it for a while.
But this type of malware was also used in the South-Korean DarkSeoul case attacking banks, and the Saoudi Aramco case attacking the oil company. Lack of international regulations made these cases also hard to classify and respond to. But while they also caused a lot of commotion, they were not considered an act of war or terrorism, nor did it result in a witch hunt.
Important to remember is Sony also has a history of leaks and security breaches. The Playstation hack of 2011 is still fresh, where 2,2 million credit card details were stolen through the Playstation network.
Yet Sony hit the panic button this time, when critical company details were compromised. The perceived gravitas was beneficial for Sony, where the attack seemed so sophisticated they would not have been able to prevent it. The idea of being ‘hacked by a dictator’ added to their benefit, where they could claim ‘circumstances beyond their control’ when they would be put on trial.It is no secret though that Sony’s security prescriptions were flawed, with the leaks even showing one of the CEO’s having an embarrassingly simple password. The panic ruled in their favour.
Bruce Schneier concludes that Sony wasn’t afraid of the damage the hackers would do in a terrorist attack, but feared for the commercial damage to the company.The leaked information is probably being sold to the highest bidder by now.
Such a perspective makes one think about the role North-Korea played in all of this. Did they really cripple a multibillion dollar company as a sadistic move because their Supreme Leader was insulted by a movie?
It is scary not to be able to tell whether an attack came from a small group of criminals playing a mean prank by releasing a threat, or an entire country. It’s causing big countries like the US to lose their cool.
Not only was the damage not that significant, was the target no matter of national security, but harsh accusations were made and sanctions were lifted against a country based on very flimsy evidence.
A long term vision is necessary to protect against cyber attacks towards the future. Especially now that the Aurora target list of American critical infrastructure was leaked.
It is highly doubtful though whether flexing some muscles and scaremongering will help to win a ‘war’ against anonymous hackers.
Biggest digital release ever
The conspiracy theorist would expose this entire debacle as an amazing marketing campaign for a movie.
Sow fear, boost patriotism, create a Barbara Streisand effect where people want to see this hyped movie. Release the movie and have everyone watch it as their personal act of rebellion. ‘That’s my kind of war on terror’ was tweeted by those proudly watching the movie.
Causing a diplomatic riot to promote a film, nothing is surprising anymore in this day and age. And whether it was deliberate or not, the film can also claim the record of the biggest digital release ever. With 15 million dollars income in the first 4 days, the movie finally catapulted the movie industry in the digital age.
The transition from 2014 to 2015 was one of many interesting phenomena. The biggest hack on American soil, fear of cyberwar and cyberterrorism, a diplomatic riot between two nuclear countries, the biggest online movie release,… All centred around one movie: The Interview. The film is definitely one for the history books, although probably not for its content.